MCP Credential Lifecycle: What Happens When Your Tokens Expire in Production
Most MCP server operators discover their token management strategy the hard way: at 2am, when an agent's tool calls start failing with auth errors and the server logs show nothing useful about why....

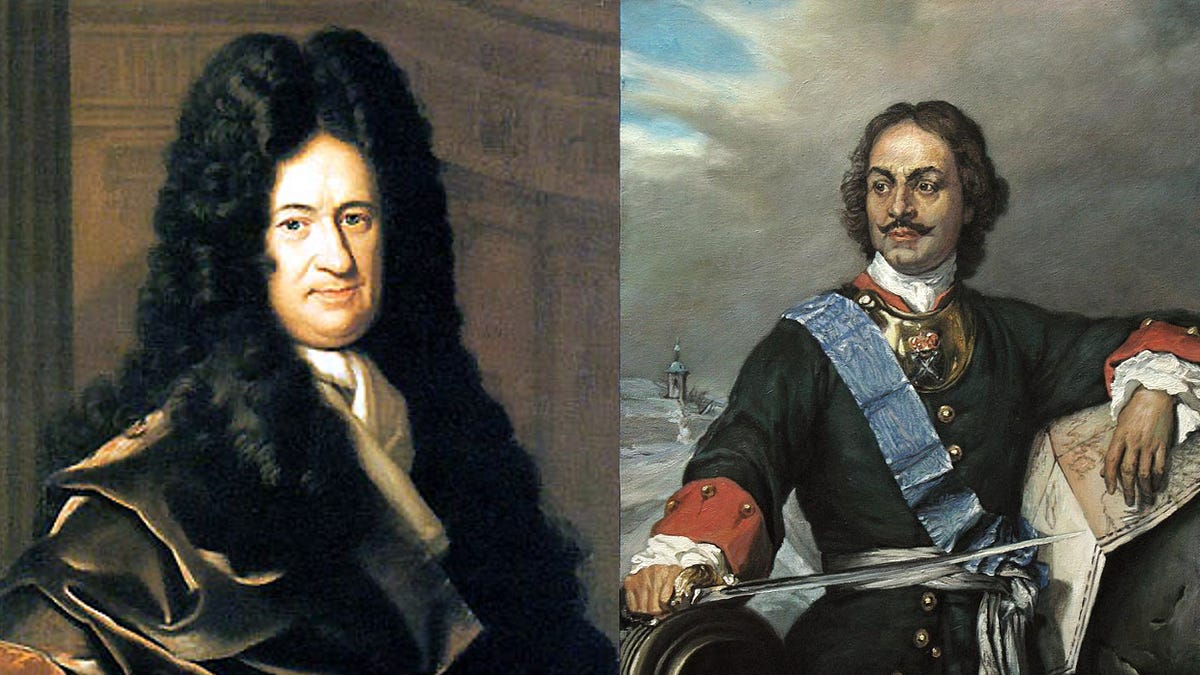
Source: DEV Community
Most MCP server operators discover their token management strategy the hard way: at 2am, when an agent's tool calls start failing with auth errors and the server logs show nothing useful about why. Credential lifecycle isn't glamorous. It's not something you add to a README. But it's the operational difference between a server that's reliable and one that fails silently whenever a token quietly expires. The Problem When an MCP server connects to upstream APIs, it holds credentials. Those credentials expire. Sometimes predictably (OAuth tokens, 1h/24h/90d depending on provider). Sometimes not — API keys revoked by admin action, NPM publish tokens that expire because the registry rotates them, service account credentials rotated by a security policy. An MCP server that doesn't handle expiry proactively is a server that waits for an agent to call a tool, get a failed response, and then... what? Retry? Fail the whole workflow? Surface an opaque error the orchestrator can't route? GitHub is